Mathematical Certainty: How TARE Uses Merkle-DAGs for Unbreakable Chain of Custody
In high-assurance laboratory environments—whether handling controlled substances, infectious agents, or critical forensic evidence—the Chain of Custody (CoC) is not just a regulatory hurdle; it's the fundamental bedrock of scientific truth.
For decades, Laboratory Information Management Systems (LIMS) have relied on standard relational databases (SQL join tables) to track where a sample came from. But in the modern threat landscape, relational tracking is vulnerable to retrospective manipulation. If an attacker (or a careless operator) gains direct database access, they can alter the history of a sample without invalidating the current state. This makes traditional audit logs little more than a "best effort" guess.
The TARE Solution: A Native Merkle-DAG
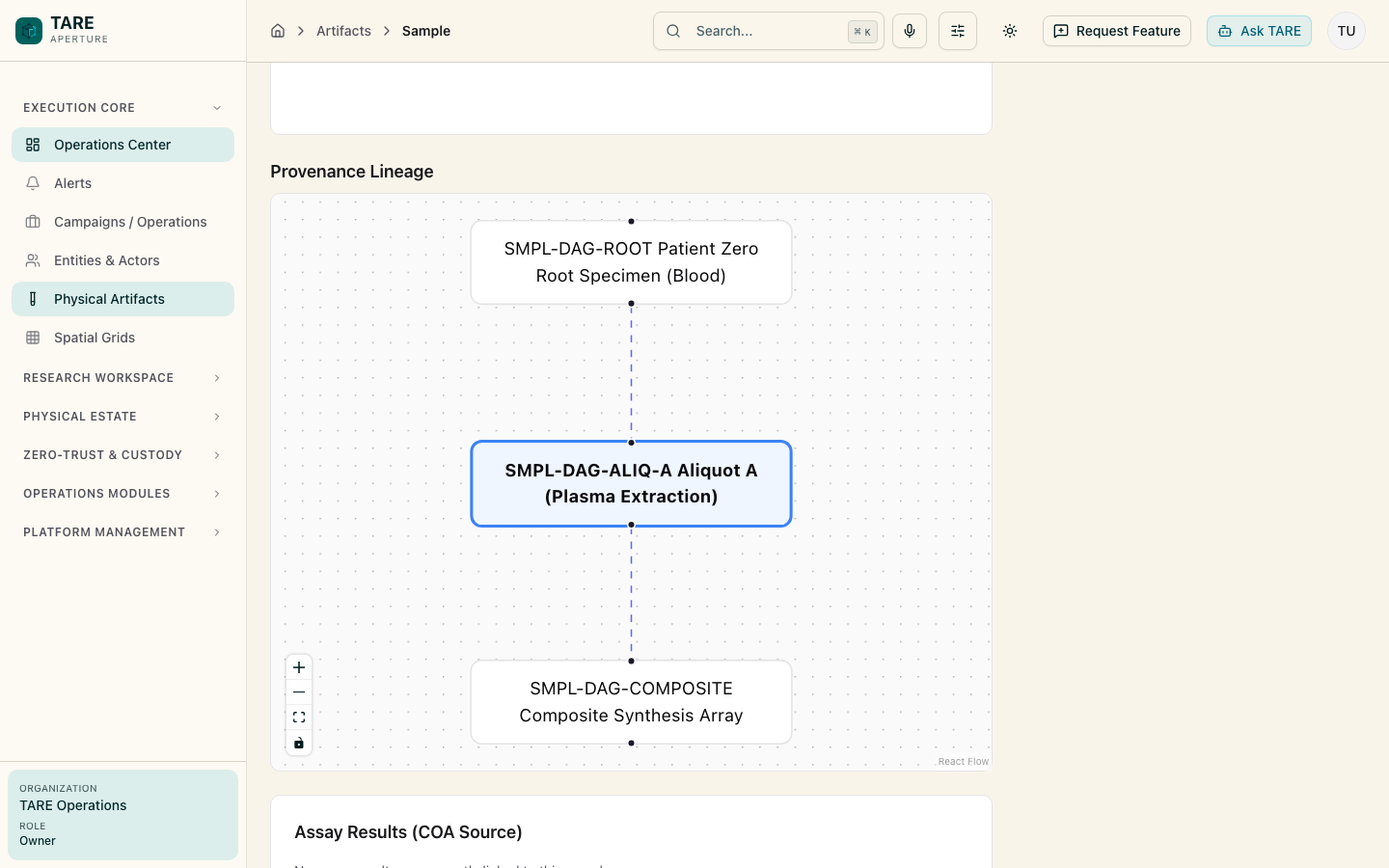
To solve this, we engineered TARE's provenance engine completely differently. Instead of flat tables, TARE models physical reality—from inventory movements to instrument observations—as a Merkle Directed Acyclic Graph (DAG).
Every action taken in the platform is sealed with an unalterable SHA-256 hash. When a derived sample is created (for example, pooling two aliquots into a synthesis array), the new node doesn't just link to a parent ID; it cryptographically hashes the signatures of all its ancestors into its own state.
Universal UUID Namespace
To make this graph seamless, all core entities in TARE (users, physical inventory locations, scientific assets, and sample tubes) utilize strict uuid identifiers natively governed by PostgreSQL. This prevents node collisions across the enterprise and allows external edge devices (like our VECTOR IoT pipeline) to asynchronously generate and sign data without requiring a round-trip to the cloud server.
Multi-Parent Convergence
Real science isn't linear. High-throughput labs frequently pool aliquots from dozens of source tubes simultaneously. TARE natively leverages deep PostgreSQL arrays (parentHashes: text[]) to stitch complex, multi-parent genealogical lineages into a single database transaction.
Why It Matters
By hashing the payload alongside all ancestor signatures, TARE natively weaves a resilient web of evidence. If any historical node is tampered with, the mathematical signatures of every child node downstream instantly invalidate.
The result? A platform where data integrity is guaranteed by math, not just policy. You don't have to trust the database administrator; you just have to trust the cryptography.